You might think free plugins are a smart way to save money and add features quickly. But have you ever stopped to consider what risks you’re inviting into your enterprise?
Behind the convenience of no-cost plugins, hidden threats like malware, data breaches, and unpatched vulnerabilities can quietly put your entire system at risk. If you value your company’s security and reputation, understanding these dangers is crucial. Keep reading to discover how free plugins can expose your business to serious security risks—and what you can do to protect your digital assets.
Credit: botscrew.com
Free plugins offer tempting benefits like cost savings and quick feature additions. Enterprises often use them to enhance system functionality without extra expenses. Yet, these plugins carry hidden security risks that can threaten enterprise data and operations.
Many free plugins lack regular updates or proper security checks. This opens doors for attackers to exploit vulnerabilities easily. Enterprises must weigh the convenience against potential threats to their systems and sensitive information.
Free plugins may contain malware or malicious code. Attackers use these to gain unauthorized access or control over enterprise systems. Some plugins come bundled with spyware or adware that steal data silently.
Outdated plugins often have known security holes. Cybercriminals scan for such weaknesses to launch attacks. Poor coding practices in free plugins can also create backdoors for hackers.
Many free plugins lack support and timely patches. This increases the risk of long-term exposure to threats. Without constant updates, vulnerabilities remain open to exploitation.
Security breaches from free plugins can disrupt business operations. Malware infections slow down or crash critical systems. Data leaks can expose sensitive customer and company information.
Compromised plugins may allow attackers to escalate privileges. This lets them control key parts of the enterprise network. Such breaches damage reputation and lead to costly recovery efforts.
Enterprises may face compliance violations due to insecure plugins. Regulatory fines and legal issues often follow data breaches. The financial and operational impact can be severe and long-lasting.
Free plugins often appear as a cost-effective solution for enterprises. Yet, they carry hidden dangers related to malware and unwanted software. These risks can disrupt operations and expose sensitive data. Understanding how malware hides in plugins helps businesses make safer choices.
Free plugins sometimes contain harmful code that activates after installation. This code can steal data, create backdoors, or damage systems. Attackers embed malicious scripts to exploit weak security in the plugin. Enterprises using such plugins risk unauthorized access and data leaks.
Many free plugins lack thorough security checks. Developers may not update them regularly, leaving vulnerabilities open. Cybercriminals target these gaps to inject malware silently. Regular audits and trusted sources reduce exposure to malicious code.
Free plugins often come with extra software hidden in the package. This bundled software may include adware, tracking tools, or unnecessary utilities. These extras slow down systems and invade privacy without clear consent.
Enterprises installing free plugins must check for bundled offers carefully. Ignoring this can lead to unwanted programs that affect network performance. Using plugins from reputable developers limits risks from bundled software.
Outdated plugins present serious security risks for enterprises. These plugins often contain old code that lacks recent security updates. Over time, hackers discover weaknesses in this code. Without timely patches, these vulnerabilities remain open doors for attacks. Enterprises relying on free plugins must understand the dangers of using outdated versions.
Many free plugins do not receive regular updates. Developers may stop maintaining them after initial release. This leaves known security flaws unpatched. Hackers can easily find and exploit these weaknesses. Unpatched flaws allow attackers to bypass security measures. They can steal data or take control of systems. Enterprises face higher risks when plugins remain outdated.
Cybercriminals actively search for outdated plugins to attack. They use automated tools to scan websites for vulnerabilities. Once found, they exploit these gaps to inject malware or ransomware. Attacks can disrupt business operations and cause financial loss. Enterprises with outdated plugins become easy targets. Regular plugin updates are essential to block cyber threats.
Data exposure and privacy concerns rank high among risks linked to free plugins. Enterprises face serious challenges protecting sensitive information. Free plugins often request broad access to website functions and user data. Without strict controls, these permissions can lead to unintended data leaks. Privacy policies of free plugins may lack clarity or be absent. This creates uncertainty about how data is stored and used. Enterprises must scrutinize plugin permissions and data handling carefully.
Many free plugins ask for permissions beyond their core function. They may request access to user accounts, files, or databases. Excessive permissions increase the risk of unauthorized data exposure. Hackers can exploit these wide permissions to breach systems. Enterprises must audit plugins to ensure permissions align with necessity. Minimizing permissions limits the attack surface and protects data.
Free plugins sometimes collect sensitive information like user details or payment data. This data can be stored insecurely or shared with third parties. Poor data protection exposes enterprises to privacy violations and legal risks. Sensitive data access by plugins demands strict vetting and monitoring. Enterprises should choose plugins with transparent privacy practices. Regular reviews help detect any suspicious data usage early.
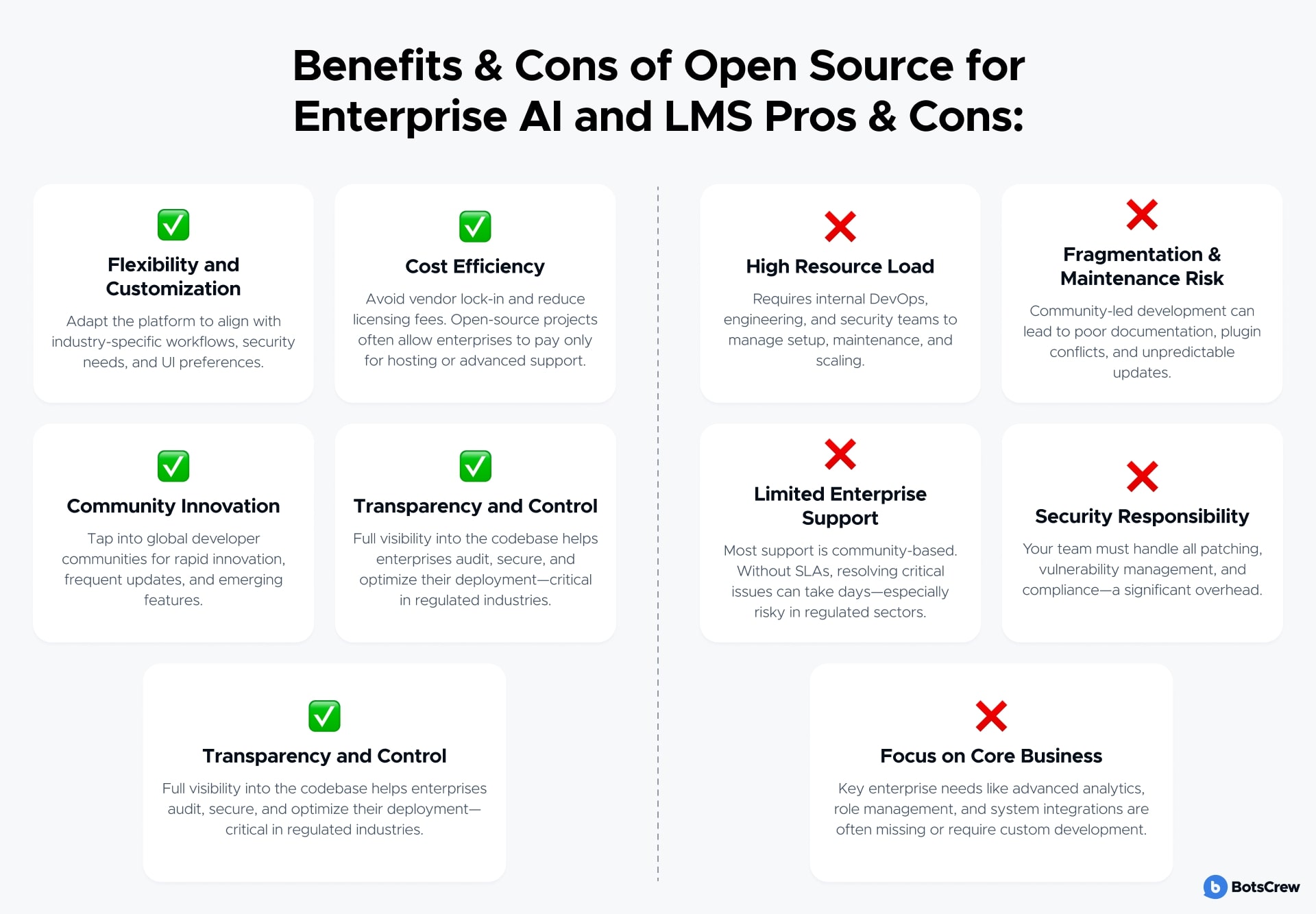
Open source plugins offer cost savings and flexibility for enterprises. Yet, they come with challenges that affect security and performance. Enterprises must carefully assess these risks before integrating such plugins into their systems.
Many open source plugins lack resources that businesses usually need. This absence can lead to significant security and operational problems.
Open source plugins often do not have dedicated support teams. Enterprises struggle to get timely help when issues arise. This delay can leave security flaws unpatched for long periods. Without expert assistance, businesses risk downtime and data breaches. Support gaps make it hard to maintain plugin security at an enterprise level.
Open source plugins may not keep pace with system updates. Compatibility problems can cause plugin failures or conflicts. Outdated plugins increase vulnerability to cyberattacks. Enterprises must invest time and resources to maintain these plugins. Without regular updates, security holes remain open and exploitable.
Free plugins often appear as a cost-effective choice for enterprises. They reduce upfront expenses and provide quick functionality. Yet, these plugins carry hidden costs that can affect security and business health. Understanding these risks helps companies make wiser decisions about plugin use.
Free plugins may lack regular updates and security patches. This leaves vulnerabilities open for hackers to exploit. Enterprises risk data breaches and unauthorized access. Many free plugins do not undergo thorough security testing. They might include malicious code or backdoors. Using such plugins can weaken overall system defenses. Security trade-offs with free plugins can lead to costly incidents.
Security issues from free plugins can damage a company’s reputation. Customers expect their data to be safe and private. A breach can destroy customer trust quickly. Negative media coverage can further harm the brand image. Restoring reputation after a security failure requires time and resources. Enterprises must consider reputation risks alongside the initial savings. The hidden costs include lost clients and reduced market confidence.
Supply chain and dependency risks pose significant challenges for enterprises using free plugins. These risks stem from the reliance on external developers and code that integrate into critical business systems. Free plugins often depend on other components, creating a complex web of dependencies that can introduce vulnerabilities. Enterprises must carefully assess these risks to protect their data and infrastructure.
Understanding how vulnerabilities spread through plugin ecosystems helps businesses manage potential threats. The risk grows as the number of dependencies increases. Even a small flaw in one plugin can compromise the entire system. Enterprises should maintain strict controls and regular audits to limit exposure to these risks.
Plugin ecosystems often include many interconnected components. Each plugin may rely on third-party libraries or frameworks, creating multiple points of failure. Attackers can exploit weaknesses in any part of this chain to gain unauthorized access.
Many free plugins lack proper security reviews or updates. This leaves known vulnerabilities open for exploitation. Enterprises face increased risk when using plugins with poor maintenance or unclear ownership. The ecosystem’s complexity makes tracking these issues difficult, increasing the chance of unnoticed risks.
Free plugins frequently use third-party code that enterprises do not control. This code may contain hidden vulnerabilities or malicious scripts. Without thorough vetting, enterprises risk introducing malware or backdoors into their systems.
Third-party code can also carry outdated dependencies. These outdated libraries might have unpatched security flaws. Enterprises should require transparency about the source and security practices of third-party components. Regular testing and scanning help identify risky code before it affects business operations.
Enterprises face serious security risks from free plugins. These risks demand strong mitigation strategies. Proper steps reduce vulnerabilities and protect critical data. Enterprises must act carefully to keep their systems safe.
Enterprises should perform regular audits of all plugins. Audits help detect outdated or vulnerable plugins early. Each plugin must be checked for security updates and compatibility. Removing unused or risky plugins lowers attack surfaces. Scheduled audits ensure continuous security monitoring.
Limiting plugin installation and management to trusted personnel is essential. Access controls prevent unauthorized changes or installations. Role-based permissions ensure only qualified staff can modify plugins. Strong authentication methods reduce risks of insider threats. These controls maintain tight security around plugin use.
Choosing plugins from reputable vendors reduces security risks. Enterprises should research plugin developers and their update history. Community feedback and ratings provide insight into plugin reliability. Avoid plugins with poor support or unknown origins. Vetting ensures the chosen plugins meet enterprise security standards.
Managing plugins effectively is vital for enterprise security. Free plugins often introduce hidden risks. Enterprises must follow strict practices to reduce vulnerabilities. Proper plugin management protects sensitive data and system integrity.
Enterprises face threats from outdated or excessive plugins. Careful control and monitoring limit potential security breaches. The following best practices help maintain a secure environment.
Regular updates fix security flaws in plugins. Enterprises should apply patches immediately after release. Ignoring updates leaves systems exposed to attacks. Automated tools can track and install updates quickly. Always test updates in a controlled setting before full deployment.
Using fewer plugins lowers the attack surface. Enterprises should install only essential plugins with trusted sources. Remove unused or outdated plugins promptly. Each additional plugin increases risk and complexity. Focus on quality rather than quantity for better security.
Monitoring tools detect unusual plugin behavior. These tools alert teams to potential threats early. Continuous scanning helps identify vulnerabilities before exploitation. Use security software compatible with your enterprise environment. Combine automated alerts with manual reviews for thorough protection.

Credit: nordlayer.com

Credit: mammothcyber.com
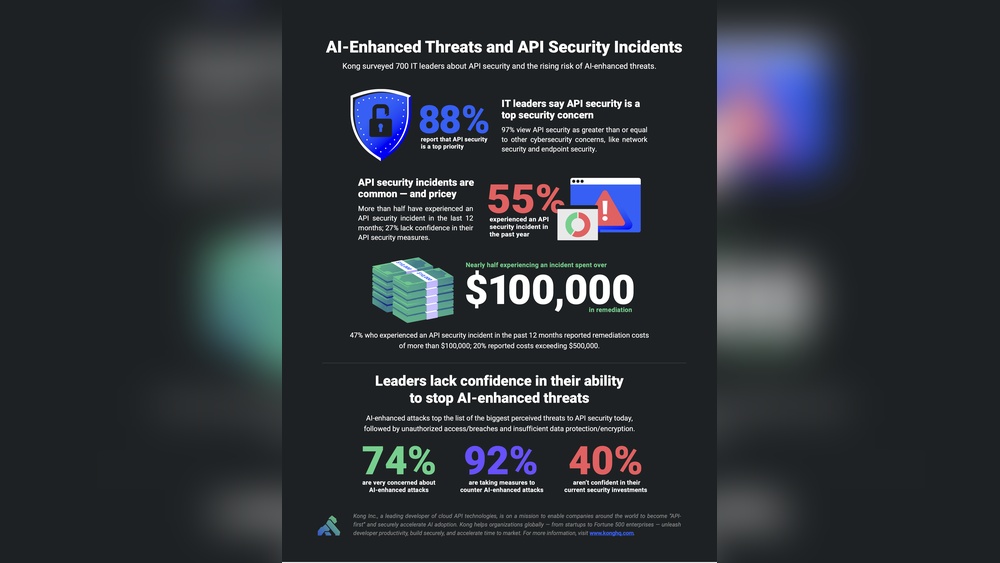
Freeware may contain malware, adware, or unwanted software that slows systems. It can expose security vulnerabilities and risk data breaches. Lack of updates increases hacking chances. Users might unknowingly grant access to sensitive information, risking privacy and account security.
Plugins pose security risks because outdated or poorly coded ones allow hackers to access websites, steal data, or inject malware. Unmaintained plugins leave vulnerabilities unpatched, increasing cyberattack chances. Granting excessive permissions can expose sensitive information, leading to account hijacking and data breaches.
Downloading extensions can expose your device to malware, data theft, and unauthorized access to sensitive information.
Open source and free software licensing can cause security vulnerabilities, lack of dedicated support, compatibility issues, and potential data breaches. Unmaintained code risks exploitation, while bundled unwanted software may affect system performance and privacy.
Free plugins may seem cost-effective but carry hidden security dangers. Enterprises risk data breaches and system compromises from unpatched vulnerabilities. Relying on unsupported or outdated plugins invites cyber threats. Always evaluate plugin sources and update regularly to reduce risks. Prioritize security over short-term savings for better protection.
Protecting your business means choosing trusted tools and staying vigilant. Remember, small weaknesses can lead to big problems. Stay informed and act wisely to keep your enterprise safe.


Leave A Reply Now