Your employee portal and login pages are gateways to sensitive company data and personal information. If they aren’t properly secured, you risk exposing your business to cyberattacks, data breaches, and unauthorized access.
But how do you protect these critical access points without making it difficult for your team to do their work? You’ll discover simple, effective strategies to lock down your employee portals and login pages. From smart authentication methods to practical security tips, you’ll learn how to keep your digital doors firmly shut against intruders—while keeping your employees safe and productive.
Keep reading to find out how you can strengthen your defenses today.
Employee portals are vital for daily business operations. They store sensitive data and enable workflow management. Such portals face many security threats. Understanding these threats helps protect your portal effectively.
Attackers use various methods to breach portals. Some threats target login pages to steal access credentials. Others exploit user sessions or come from inside the organization. Knowing these common threats is key to securing employee portals.
Phishing tricks employees into revealing usernames and passwords. Fake emails or websites mimic real portals. Users enter their credentials, which attackers capture. Stolen credentials let attackers access the portal as trusted users.
Credential theft also happens through malware or keyloggers. Attackers use these tools to record login details silently. Protecting against phishing and malware reduces risks significantly.
Brute force attacks guess passwords by trying many combinations. Automated tools speed up this process. Weak or common passwords make brute force attacks easy to succeed. Attackers gain access by cracking simple login credentials.
Strong password policies and login attempt limits help stop brute force attacks. Monitoring unusual login attempts also helps detect such threats early.
Session hijacking steals active user sessions after login. Attackers capture session cookies or tokens to impersonate users. This bypasses password entry and grants full access. Public Wi-Fi and insecure networks increase this risk.
Using secure connections and short session timeouts limits session hijacking. Encryption and multi-factor authentication add extra protection.
Insider threats come from employees or contractors with portal access. These insiders may misuse their privileges intentionally or by accident. They can leak data, change information, or create backdoors.
Strict access controls and regular audits reduce insider risks. Training staff on security policies also lowers chances of accidental breaches.
Strengthening authentication is essential for protecting employee portals and login pages. It limits access to authorized users only. Strong authentication reduces risks of data breaches and unauthorized entry.
Simple passwords no longer offer enough security. Modern methods add extra layers to verify user identity. These methods make it harder for attackers to impersonate employees.
Multi-factor authentication (MFA) requires users to provide two or more proofs of identity. This can include a password plus a code sent to a phone. MFA stops attackers who steal passwords alone. It is one of the most effective security tools.
Passwordless login removes the need for traditional passwords. Users can log in using email links or one-time codes. This method cuts risks of weak or reused passwords. It also improves user experience by simplifying access.
Biometric authentication uses unique physical traits like fingerprints or face scans. These traits are hard to copy or steal. Biometric data adds strong security and convenience. It works well on mobile devices and modern computers.
Token-based systems issue a temporary digital token after login. Users present the token for future access without re-entering credentials. Tokens can expire or be revoked quickly. This limits the time attackers can misuse stolen tokens.
Protecting login pages is vital for securing employee portals. These pages are the main gateway to sensitive company data. Attackers often target login pages to steal credentials or gain unauthorized access. Strengthening these pages reduces security risks and helps maintain trust within the organization.
Simple measures can prevent many common attacks. Making login pages resilient stops attackers early. Let’s explore key steps to protect login pages effectively.
CAPTCHA blocks automated bots from abusing login pages. It asks users to solve puzzles that humans find easy but bots cannot. This prevents brute force attacks that try many password combinations quickly. Using CAPTCHA adds a layer of defense without much inconvenience for real users.
Username enumeration occurs when attackers discover valid usernames through error messages. Login pages must avoid revealing if a username exists or not. Use generic error messages like “Invalid login credentials” for all failed attempts. This stops attackers from learning which usernames to target.
Rate limiting restricts how many login attempts happen in a short time. Lockouts temporarily block accounts after several failed tries. These methods slow down attackers trying many passwords quickly. They also alert admins to suspicious activity. Proper settings balance security with user convenience.
SSL/TLS encrypts data between users and the server. This protects login information from being intercepted. Use strong, up-to-date SSL/TLS protocols and ciphers. Avoid outdated versions like SSL 3.0 or TLS 1.0. Always enforce HTTPS on login pages to keep data safe during transmission.
Securing user credentials is a key step in protecting employee portals and login pages. Usernames and passwords are the main gatekeepers to sensitive company data. Weak credentials can lead to unauthorized access and data breaches. Strong measures ensure only authorized users can enter the system.
Focus on creating solid password rules, safe storage methods, and regular checks. These actions reduce risks and strengthen portal security. Let’s explore how to secure user credentials effectively.
Set clear rules for passwords. Require a mix of letters, numbers, and symbols. Avoid common words or easy patterns. Enforce minimum length, such as eight characters or more. Require regular password changes to prevent long-term exposure. Teach employees to avoid password reuse across accounts. These steps make guessing or cracking passwords much harder.
Never store passwords as plain text. Use strong hashing algorithms like bcrypt or Argon2. Hashing converts passwords into unreadable codes. Add a unique salt to each password before hashing. This prevents attackers from using precomputed hash tables. Secure storage protects credentials even if the database is breached.
Conduct frequent reviews of user credentials. Identify weak or outdated passwords. Detect inactive accounts that may pose risks. Remove or disable accounts no longer in use. Use automated tools to scan for compromised credentials. Regular audits keep the system clean and reduce attack surfaces.
Monitoring and detection play a vital role in securing employee portals and login pages. Continuous observation helps spot unauthorized access attempts early. Effective monitoring tools provide detailed insights into user activity. Detection systems analyze patterns to identify threats before damage occurs. Together, these methods strengthen portal security and protect sensitive data.
Track all login attempts to your employee portal. Record user ID, time, location, and device used. This data helps spot unusual access trends quickly. Regular review of login logs aids in identifying breaches. Automated systems can store and analyze this information securely.
Use analytics to detect unusual user behavior patterns. Compare current activity against typical user actions. Alerts can trigger if an employee logs in from a new device or location. Behavioral analytics spot potential threats that simple logs miss. This approach helps detect insider threats and compromised accounts.
Set up real-time alerts for suspicious login attempts. Notify security teams instantly when risks appear. Alerts can include multiple failed logins or access from blacklisted IPs. Quick response to alerts reduces breach impact. Customize alert settings to suit your company’s risk level.

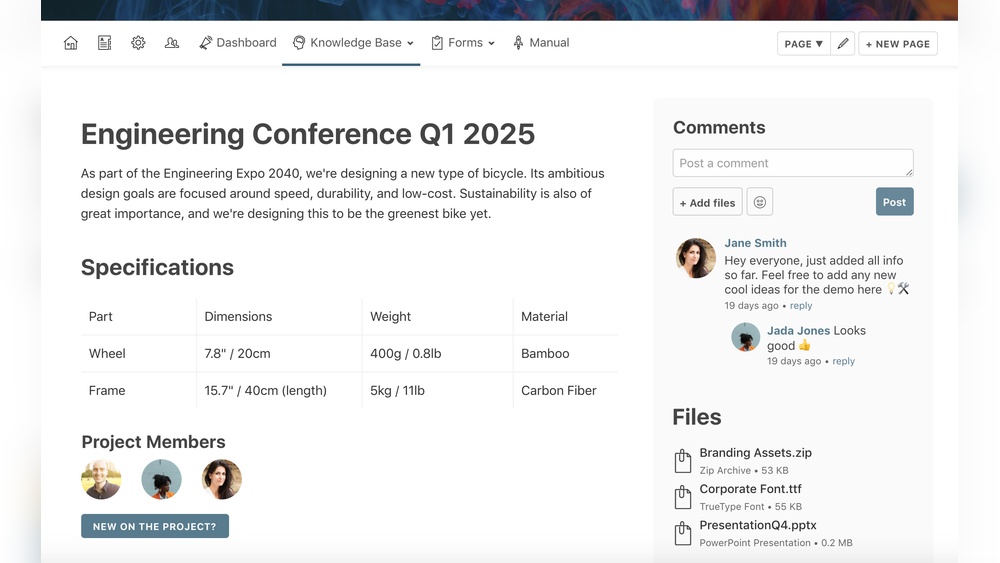
Credit: budibase.com
Network and infrastructure security forms the backbone of protecting employee portals and login pages. Strong defenses at this level stop many attacks before they reach the application. Securing the network reduces risks from unauthorized access and data breaches. It also ensures that only trusted users and devices connect to sensitive systems.
Implementing proper network controls helps maintain the integrity and confidentiality of employee data. The following key components play vital roles in network and infrastructure security.
Firewalls act as barriers between trusted internal networks and untrusted external networks. They monitor and filter incoming and outgoing traffic based on security rules. Properly configured firewalls block malicious traffic and allow legitimate connections.
Proxy servers serve as intermediaries between users and the internet. They can hide internal IP addresses and filter content. Using proxies adds an extra layer of protection and helps enforce security policies on employee portals.
DNS filtering blocks access to harmful or unauthorized websites by filtering domain name requests. This prevents employees from reaching phishing sites or malware-hosting domains. DNS filtering also reduces the risk of data leakage.
Access controls restrict network resources to authorized users only. Setting strong permissions limits who can access the portal and what actions they can perform. Combining DNS filtering with access controls strengthens portal security.
Servers hosting employee portals must be configured securely to reduce vulnerabilities. Disable unused services and close unnecessary ports. Regularly update software and apply security patches.
Use encryption protocols like TLS to protect data in transit. Set up strong authentication methods for server access. These steps prevent attackers from exploiting weak server settings.
Training employees and setting clear policies form the backbone of secure portals and login pages. Users must understand security risks and best practices. Well-informed employees reduce the chance of breaches caused by human error.
Regular training and written policies help maintain security awareness. Everyone should know their role in protecting company data. Clear rules guide proper portal use and prevent careless mistakes.
Security awareness programs teach employees about threats like phishing and weak passwords. Short sessions with examples make lessons easy to remember. Repeating training keeps security top of mind. Employees learn how to spot suspicious emails or links. Simple tips like using strong passwords protect accounts effectively.
Access policies define who can use the portal and what they can do. Limit login rights to necessary employees only. Explain password rules, session timeouts, and device restrictions. Written policies help avoid confusion and risky behaviors. Everyone must follow the same rules to keep data safe.
Employees need clear instructions on reporting security problems. Quick reporting stops attacks from spreading. Provide easy ways to report issues like suspicious emails or login failures. Train staff to act calmly and report promptly. Early detection protects the entire system.

Credit: dribbble.com
Advanced security measures protect employee portals and login pages from evolving cyber threats. These strategies go beyond basic passwords and simple authentication. They ensure that only authorized users gain access to sensitive information. Implementing these measures reduces the risk of data breaches and unauthorized entry.
Employers must adopt modern technologies to keep employee portals safe. These include methods that adapt to user behavior and limit access based on need and time. This section explores key techniques that enhance portal security effectively.
Just-in-Time (JIT) access limits user permissions to only what is needed at the moment. Users receive access rights temporarily, reducing exposure to sensitive data. Once the task is complete, access is revoked automatically. This minimizes the window for potential misuse or attacks.
JIT access helps control who can view or modify information. It also supports compliance with strict data protection rules. By granting access only when necessary, organizations reduce insider threats and accidental leaks.
Behavioral biometric authentication identifies users by their unique behavior patterns. This includes typing speed, mouse movements, and navigation habits. It creates a profile for each user to detect anomalies during login.
This method adds a layer of security without frustrating users. If the system notices unusual behavior, it can block access or require extra verification. Behavioral biometrics help prevent account takeovers and fraud.
Passwordless authentication removes the need for traditional passwords. Instead, users log in using biometrics, security keys, or one-time codes. This reduces the risk of stolen or weak passwords.
Popular trends include using fingerprint scanners, facial recognition, and mobile device prompts. These methods provide fast, secure access and improve user experience. Organizations adopting passwordless solutions lower the chances of phishing and credential theft.

Credit: www.salesforce.com
Secure a login page by enforcing strong passwords and multi-factor authentication. Use HTTPS to encrypt data. Implement brute-force protection and prevent username enumeration. Regularly update software and monitor for suspicious activity to enhance security.
The most secure login method uses multi-factor authentication (MFA) combining passwords with biometrics or tokens. Passwordless logins and passkeys also enhance security by reducing password risks. These methods prevent unauthorized access while keeping user experience smooth and safe.
Use network tools like DNS filtering, firewalls, or proxy servers to block websites company-wide. Install web filtering software or browser extensions on devices for added control. Set clear policies and train employees to support technical restrictions effectively.
Use strong, unique passwords and change them regularly. Enable multi-factor authentication for extra security. Store credentials in encrypted password managers. Avoid sharing passwords and monitor login activity. Educate users on phishing and secure login habits.
Securing employee portals and login pages protects company data and users. Use strong passwords and enable multi-factor authentication for better safety. Regularly update software to fix security weaknesses. Monitor login attempts to detect suspicious activity early. Educate employees about safe login habits and phishing risks.
Simple steps create a safer digital workplace for everyone. Stay proactive to keep your portals secure and trusted.


Leave A Reply Now